Single Sign-On Integration
Bright Pattern integrates with Security Assertion Markup Language (SAML) 2.0 identity providers, allowing you to configure single sign-on (SSO) functionality for the Agent Desktop application, and optionally, the Contact Center Administrator (Admin) application.
For specific instructions on configuring SSO with specific providers, see the Single Sign-On Integration Guide.
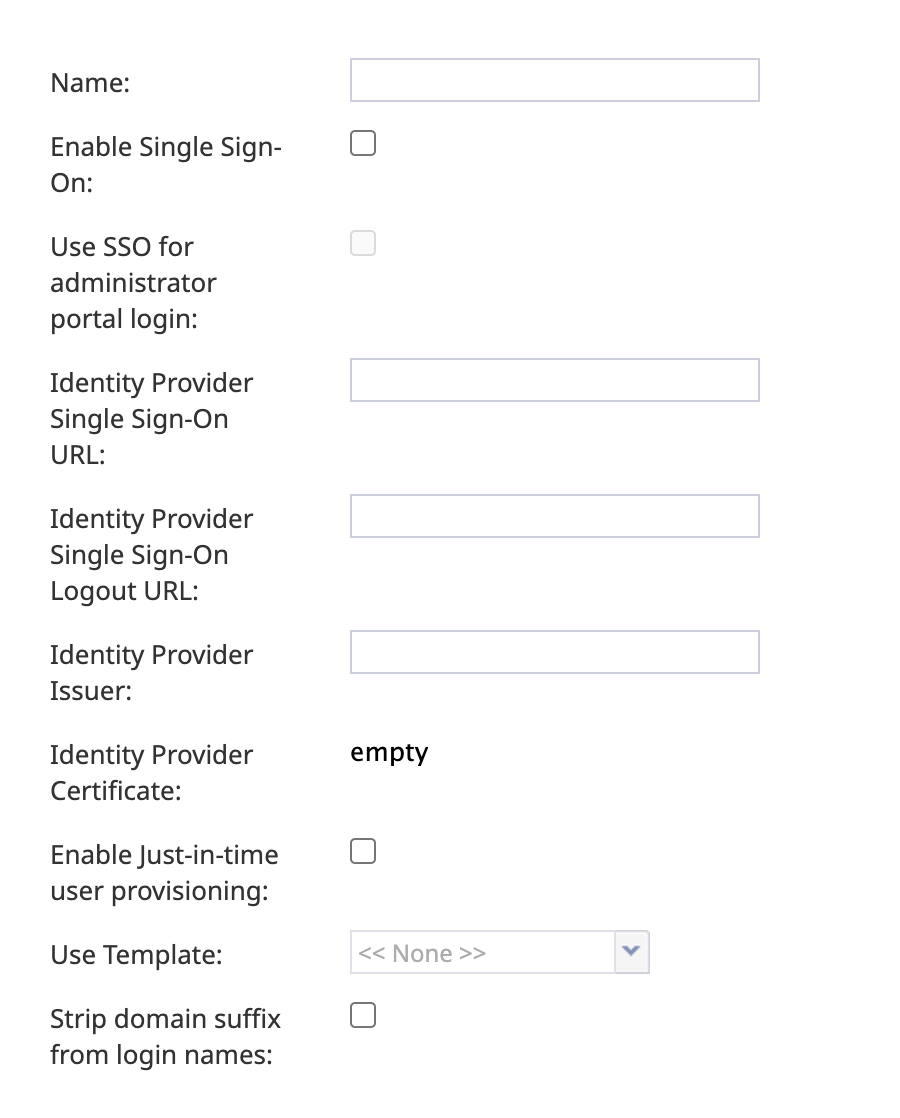
| ||
Properties
Name
The name of the integration account (any name).
Enable Single Sign-On
Select the checkbox to enable single sign-on functionality for the Agent Desktop application.
Use SSO for administrator portal login
Select the checkbox in order to enable SSO for users of the Contact Center Administrator application (i.e., the "administrator portal") who have the admin role.
Identity Provider Single Sign-On URL
The login URL of your identity provider.
Identity Provider Single Sign-On Logout URL
The URL used to initiate logout from your identity provider. Note that this is not the logout URL that can be configured in some identity providers, which configures a URL to redirect users to after the logout operation is completed.
Identity Provider Issuer
The unique identifier of your identity provider.
Identity Provider Certificate
The contents of the SAML certificate that the identity provider uses to sign the SAML tokens that it sends to the application.
Enable Just-in-time user provisioning
Select this checkbox to enable Just-in-time user provisioning (JIT). JIT user provisioning automatically creates call center users on the first SSO login attempt authorized by the identity provider.
You should enable JIT user provisioning if:
- JIT user provisioning is enabled for the application
- The tenant URL is known (extracted from the domain name, tenantUrl parameter, or SAML additional parameter)
- The user with login Id does not exist in that tenant
- SAML assertion is signed and valid
When creating a new user using JIT user provisioning:
- The newly created user should copy assignments (e.g., roles, teams, skills, etc.) from the selected user template
- User contact information should be copied from SAML assertion. As a minimum, this contact information should include first name, last name, login ID, and email address (others are optional)
- Once the user is created, that user should be logged in immediately
Use Template
Select this checkbox to copy assignments (e.g., roles, teams, skills, etc.) from a specific user, and apply them to new call center users created by JIT user provisioning.
Note that SSO templates are only used when just-in-time user provisioning is enabled.
Strip domain suffix from login names
When this checkbox is selected, this option removes the domain suffix from user logins. For example, jane.doe@website.com would be converted to simply jane.doe. If the box is unchecked, the full login name will be used. This box is unchecked by default.