(Marked this version for translation) |
(Updated via BpDeleteTranslateTags script) |
||
| Line 1: | Line 1: | ||
| − | + | = Single Sign-On Integration = | |
Bright Pattern integrates with Security Assertion Markup Language (SAML) 2.0 identity providers, allowing you to configure single sign-on (SSO) functionality for the Agent Desktop application or the Contact Center Administrator (Admin) application. | Bright Pattern integrates with Security Assertion Markup Language (SAML) 2.0 identity providers, allowing you to configure single sign-on (SSO) functionality for the Agent Desktop application or the Contact Center Administrator (Admin) application. | ||
| − | |||
Note that only one instance can be created per contact center. | Note that only one instance can be created per contact center. | ||
| − | |||
Note that SSO bypass is allowed by privilege. For more information, see section [[Contact-center-administrator-guide/UsersandTeams/Privileges#Bypass_Single_Sign-On|Privileges]]. | Note that SSO bypass is allowed by privilege. For more information, see section [[Contact-center-administrator-guide/UsersandTeams/Privileges#Bypass_Single_Sign-On|Privileges]]. | ||
| − | |||
For specific instructions on configuring SSO with specific providers see ''Administration Tutorials'', section [[Tutorials-for-admins/AboutIntegrations|Integrations]]. | For specific instructions on configuring SSO with specific providers see ''Administration Tutorials'', section [[Tutorials-for-admins/AboutIntegrations|Integrations]]. | ||
| − | == Properties == | + | == Properties == |
There are two types of properties for Single Sign-On integration accounts: Agent Desktop SSO and Admin SSO. You can enable just Agent Desktop SSO functionality and keep Admin login credentials local or you can enable both Agent Desktop and Admin SSO functionality. | There are two types of properties for Single Sign-On integration accounts: Agent Desktop SSO and Admin SSO. You can enable just Agent Desktop SSO functionality and keep Admin login credentials local or you can enable both Agent Desktop and Admin SSO functionality. | ||
| − | |||
[[File:CCA-Integration-Accounts-Single-Sign-On-Settings-2-5399scim.PNG|450px|thumbnail|center|Single Sign-On integration account properties]] | [[File:CCA-Integration-Accounts-Single-Sign-On-Settings-2-5399scim.PNG|450px|thumbnail|center|Single Sign-On integration account properties]] | ||
| − | === Name === | + | === Name === |
The name of the integration account (any name). | The name of the integration account (any name). | ||
| − | === Enable Single Sign-On === | + | === Enable Single Sign-On === |
Select the checkbox to enable single sign-on functionality for the Agent Desktop application. | Select the checkbox to enable single sign-on functionality for the Agent Desktop application. | ||
| − | === Use SSO for administrator portal login === | + | === Use SSO for administrator portal login === |
Select the checkbox in order to enable SSO for users of the Contact Center Administrator application (i.e., the "administrator portal") who have the admin role. | Select the checkbox in order to enable SSO for users of the Contact Center Administrator application (i.e., the "administrator portal") who have the admin role. | ||
| − | === Identity Provider Single Sign-On URL === | + | === Identity Provider Single Sign-On URL === |
The login URL of your identity provider. | The login URL of your identity provider. | ||
| − | === Identity Provider Issuer === | + | === Identity Provider Issuer === |
The unique identifier of your identity provider. | The unique identifier of your identity provider. | ||
| − | === Identity Provider Certificate === | + | === Identity Provider Certificate === |
The contents of the SAML certificate that the identity provider uses to sign the SAML tokens that it sends to the application. | The contents of the SAML certificate that the identity provider uses to sign the SAML tokens that it sends to the application. | ||
| − | === Enable Just-in-time user provisioning === | + | === Enable Just-in-time user provisioning === |
Select this checkbox to enable Just-in-time user provisioning (JIT). JIT user provisioning automatically creates call center users on the first SSO login attempt authorized by the identity provider. | Select this checkbox to enable Just-in-time user provisioning (JIT). JIT user provisioning automatically creates call center users on the first SSO login attempt authorized by the identity provider. | ||
| − | |||
Note that JIT is disabled if SSO is not enabled. | Note that JIT is disabled if SSO is not enabled. | ||
| − | |||
You should enable JIT user provisioning if: | You should enable JIT user provisioning if: | ||
* JIT user provisioning is enabled for the application | * JIT user provisioning is enabled for the application | ||
| Line 50: | Line 44: | ||
* SAML assertion is signed and valid | * SAML assertion is signed and valid | ||
| − | |||
When creating a new user using JIT user provisioning: | When creating a new user using JIT user provisioning: | ||
* The newly created user should copy assignments (e.g., roles, teams, skills, etc.) from the selected user template | * The newly created user should copy assignments (e.g., roles, teams, skills, etc.) from the selected user template | ||
| Line 56: | Line 49: | ||
* Once the user is created, that user should be logged in immediately | * Once the user is created, that user should be logged in immediately | ||
| − | === Use Template === | + | === Use Template === |
Select this checkbox to copy assignments (e.g., roles, teams, skills, etc.) from a specific user, and apply them to new call center users created by JIT user provisioning. | Select this checkbox to copy assignments (e.g., roles, teams, skills, etc.) from a specific user, and apply them to new call center users created by JIT user provisioning. | ||
| − | + | Note that SSO templates are required if JIT user provisioning enabled. SSO templates are disabled if JIT user provisioning is disabled. | |
| − | Note that SSO templates are required if JIT user provisioning enabled. SSO templates are disabled if JIT user provisioning is disabled. | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
Latest revision as of 04:08, 29 May 2024
Single Sign-On Integration
Bright Pattern integrates with Security Assertion Markup Language (SAML) 2.0 identity providers, allowing you to configure single sign-on (SSO) functionality for the Agent Desktop application or the Contact Center Administrator (Admin) application.
Note that only one instance can be created per contact center.
Note that SSO bypass is allowed by privilege. For more information, see section Privileges.
For specific instructions on configuring SSO with specific providers see Administration Tutorials, section Integrations.
Properties
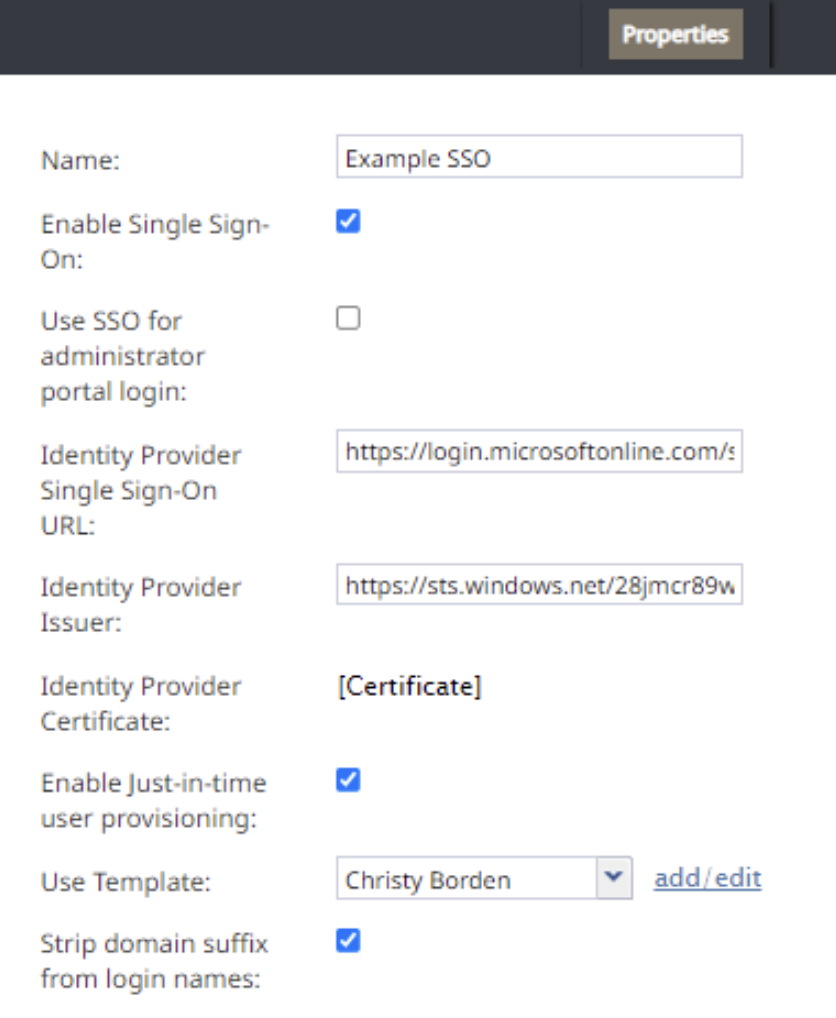
There are two types of properties for Single Sign-On integration accounts: Agent Desktop SSO and Admin SSO. You can enable just Agent Desktop SSO functionality and keep Admin login credentials local or you can enable both Agent Desktop and Admin SSO functionality.
Name
The name of the integration account (any name).
Enable Single Sign-On
Select the checkbox to enable single sign-on functionality for the Agent Desktop application.
Use SSO for administrator portal login
Select the checkbox in order to enable SSO for users of the Contact Center Administrator application (i.e., the "administrator portal") who have the admin role.
Identity Provider Single Sign-On URL
The login URL of your identity provider.
Identity Provider Issuer
The unique identifier of your identity provider.
Identity Provider Certificate
The contents of the SAML certificate that the identity provider uses to sign the SAML tokens that it sends to the application.
Enable Just-in-time user provisioning
Select this checkbox to enable Just-in-time user provisioning (JIT). JIT user provisioning automatically creates call center users on the first SSO login attempt authorized by the identity provider.
Note that JIT is disabled if SSO is not enabled.
You should enable JIT user provisioning if:
- JIT user provisioning is enabled for the application
- The tenant URL is known (extracted from the domain name, tenantUrl parameter, or SAML additional parameter)
- The user with login Id does not exist in that tenant
- SAML assertion is signed and valid
When creating a new user using JIT user provisioning:
- The newly created user should copy assignments (e.g., roles, teams, skills, etc.) from the selected user template
- User contact information should be copied from SAML assertion. As a minimum, this contact information should include first name, last name, login ID, and email address (others are optional)
- Once the user is created, that user should be logged in immediately
Use Template
Select this checkbox to copy assignments (e.g., roles, teams, skills, etc.) from a specific user, and apply them to new call center users created by JIT user provisioning.
Note that SSO templates are required if JIT user provisioning enabled. SSO templates are disabled if JIT user provisioning is disabled.